The Cybersecurity Podcast Network - Security Weekly | SC Media


For Security Professionals by Security Professionals
Subscribe and listen on the go
Our Shows
Paul's Security Weekly
Unpacking the latest IT security news, vulnerabilities, and research through a historical and technical lens that can cut through even the thickest cigar smoke.
Watch NowEnterprise Security Weekly
Enterprise security news, insights, and vendor analysis to explore the latest trends that can help defenders succeed.
Watch NowBusiness Security Weekly
About bridging the gap between security initiatives and business objectives.
Watch NowApplication Security Weekly
About all things AppSec, DevOps, and DevSecOps focusing on helping its audience find and fix software flaws effectively.
Watch NowSecurity Weekly News
Concise, bi-weekly reviews of the most significant security stories, including malware, threats, government actions, and other cybersecurity topics.
Watch Now
Stay Ahead with Exclusive Security Insights
Join The Security Weekly Insider List
Recent Episodes
Join Our Community
We would love your support in enhancing our podcast! If you’re interested in becoming a sponsor or have a guest recommendation, please reach out. Your contribution can make a meaningful impact!
Our Hosts
Paul Asadoorian
Eclypsium, Principal Security Researcher
Host - Paul's Security Weekly
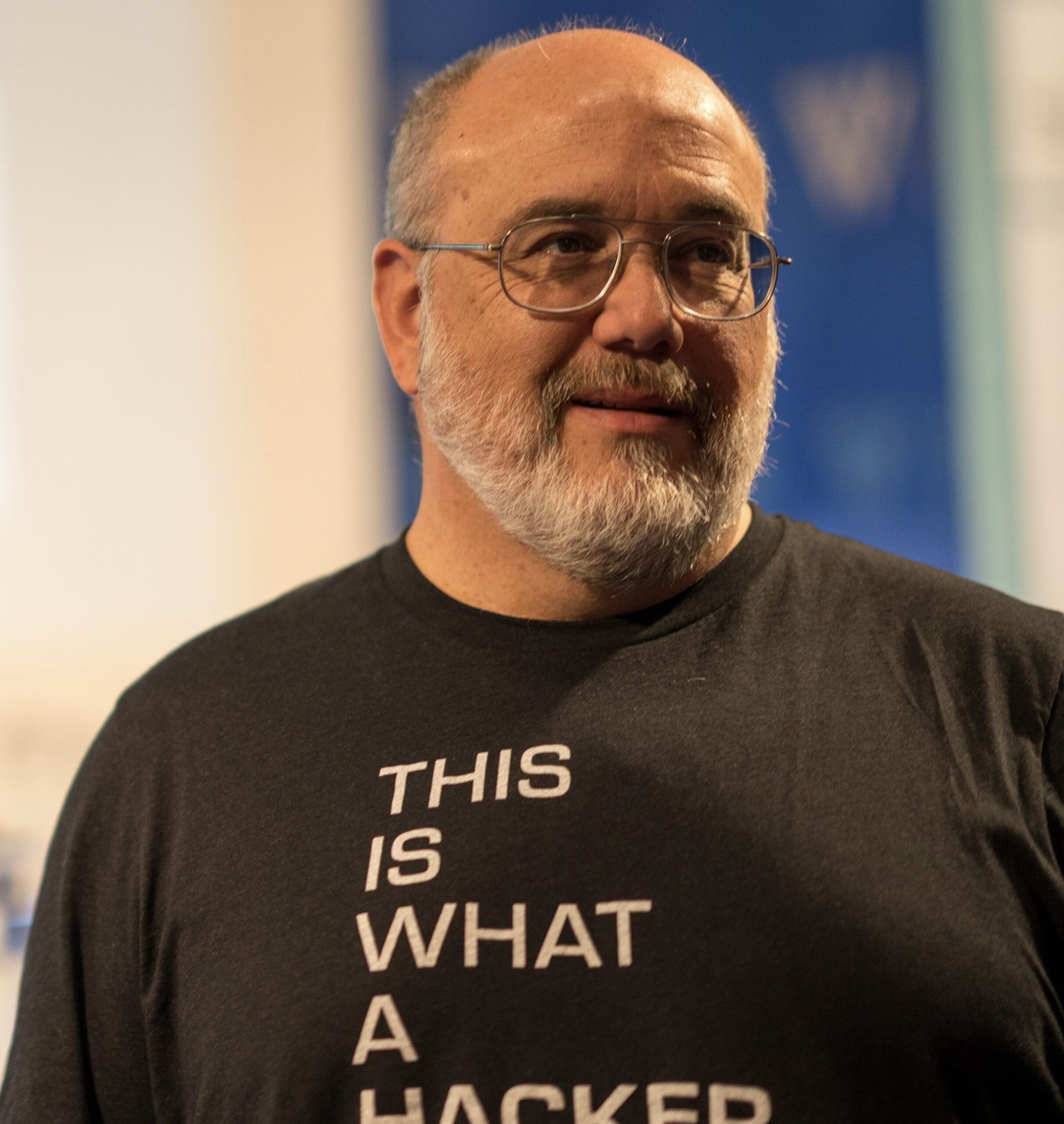
Larry Pesce
Finite State, Vice President of Services
Host - Paul's Security Weekly
You can skip this ad in 5 seconds